Why WordPress audits keep finding the same things
WordPress is the most common CMS on the planet — depending on which survey you trust, it powers 40-43% of all live websites in 2026. That ubiquity means a couple of things for someone doing audits: most issues are recurring patterns (every WP site has the same potential problems), and most issues are fixable without touching code.
This article walks through the eight free tools I run on every WordPress audit, the specific issues each tool surfaces, and the order to do them in. The full audit takes 60-90 minutes for a 50-page WordPress site. Nothing here requires plugin installation or admin access to the WordPress site itself — every tool operates from the outside in.
A note on bias: I run Krawly. Most of the tools below are mine. Where a non-Krawly tool is more useful for the specific step, I name it.
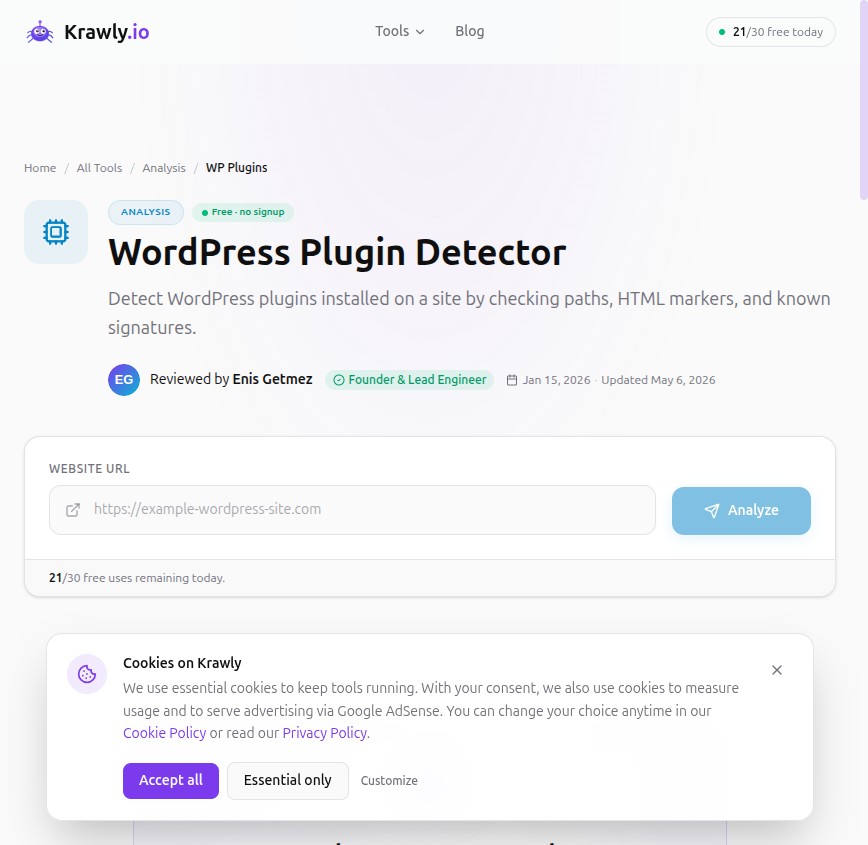
Step 1: Plugin inventory ([WordPress Plugin Detector](/tool/wordpress-plugin-detector))
WordPress sites are mostly defined by their plugins. The plugin set tells you the site's caching layer, SEO approach, e-commerce stack, security posture, and accessibility maturity. Plugin Detector reads the public HTML for plugin-specific signatures (asset URLs, generator meta tags, distinctive class names) and surfaces what's installed.
Patterns I look for:
The single highest-impact finding I see: multiple SEO plugins installed simultaneously (Yoast + Rank Math, or Yoast + All in One). Both inject their own meta tags, which fight for the og:title and og:description outputs. The site ends up with duplicate or contradictory meta. Disable one.
Step 2: Theme + WordPress version detection
The same plugin detector usually surfaces the theme name and (sometimes) WordPress core version. If the version is older than the current major release minus 1 (so today, in May 2026, anything older than WP 6.6 if 6.7 is current), the site is missing 12+ months of security patches.
WordPress core auto-updates handle minor versions (6.7.1, 6.7.2). Major version updates require opting in — which many sites never do. Outdated major versions don't just mean missing features; they mean missing security fixes.
How to confirm: check the `generator` meta tag in the page source. `` is the explicit answer.
Step 3: Meta tag and schema audit ([Meta Tag Validator](/tool/meta-tag-validator) + [Structured Data Validator](/tool/structured-data-validator))
WordPress sites with an active SEO plugin usually have decent meta tags. WordPress sites with a misconfigured SEO plugin have catastrophic ones.
What I look for:
The single most common WordPress meta issue: the theme's custom title format overrides the SEO plugin's. Yoast tells you the title should be "Post Name | Site Name". The theme outputs "Site Name — Post Name". When both fight, the theme usually wins because it loads later. Auditing the rendered title vs the configured title is a 1-minute check.
For WooCommerce, run Structured Data Validator on a product URL and confirm a valid `Product` JSON-LD block with price + availability + image. My recent 50-store schema audit covers the patterns in depth.
Step 4: Performance audit ([Page Speed Analyzer](/tool/page-speed-analyzer) + Lighthouse)
Most WordPress performance issues come from one of three categories:
1. Render-blocking JS in the head — themes that inject jQuery, Google Tag Manager, or Facebook Pixel synchronously
2. Unoptimised hero images — 4000×3000 JPEGs as featured images, served without WebP fallback
3. Database queries per page request — caching plugin off or misconfigured
`Page Speed Analyzer` will surface #1 and #2 from outside. #3 is invisible from outside but inferable: if first-byte time (TTFB) is over 1 second consistently, the origin is doing expensive work per request. The fix is caching.
For #1, the common WordPress fix is "Defer / Async" toggles in the cache plugin. WP Rocket, LiteSpeed Cache, and Autoptimize all expose this. Toggle it, test the site for breakage (jQuery-dependent themes break sometimes), keep it on.
For #2, every WordPress site should have an image optimization plugin in 2026 — Smush, ShortPixel, EWWW Image Optimizer, or Imagify. All have free tiers covering the first few thousand images. WebP conversion drops image weights by 30-40% on average.
Step 5: Broken link sweep ([Broken Link Checker](/tool/broken-link-checker))
WordPress sites accumulate broken links faster than most platforms — every WordPress post has typically 3-10 outbound links to other sources, and those sources rot at 5-10% per year. After 5 years a post has 20-40% broken outbound links unless someone has maintained it.
The audit:
1. Run Broken Link Checker on your top 10 traffic-driving posts (per Google Search Console).
2. For each broken outbound link, either replace it with a current alternative, link to a Wayback Machine snapshot via Wayback Checker, or remove it.
3. Update the post's "last modified" date so Google re-crawls.
This is 1-2 hours per audit. Counter-intuitively, this is among the highest-ROI SEO maintenance for an established blog — Google measurably weights "fresh, well-maintained content" over "old stale content" even when the underlying message hasn't changed.
Step 6: Comment spam / form spam check
WordPress sites often expose AJAX endpoints (`wp-admin/admin-ajax.php`) and comment endpoints to anonymous traffic. These are spam magnets and sometimes vulnerability surfaces.
Quick checks from outside:
Most WordPress security plugins handle this; sites without one are obvious.
Step 7: HTML scraping for visible content quality ([CSS Selector Scraper](/tool/css-selector-scraper))
This is the meta-audit. For your top 10 pages, scrape just the heading content:
```
https://example.com/blog/some-post|||h1, h2, h3
```
What you should see:
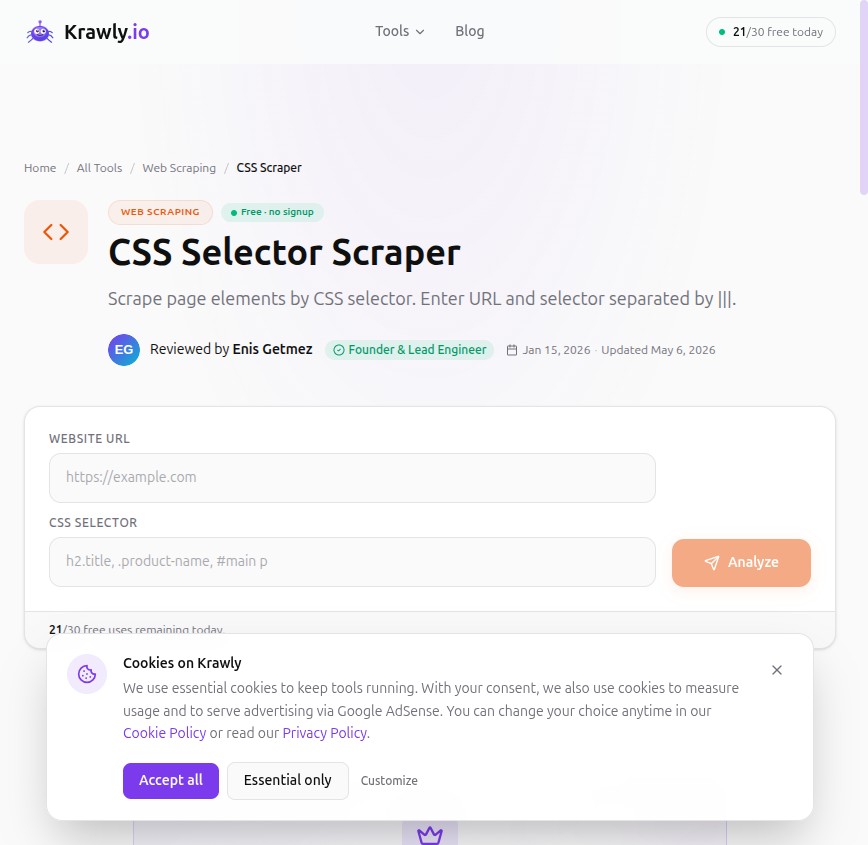
WordPress themes are infamous for breaking heading order. The Gutenberg block editor sometimes inserts H2s where authors intended H3s. The Classic Editor often had authors mis-using H1 multiple times per page. Both still happen on legacy posts.
Step 8: Security headers grade ([HTTP Security Headers Grader](/tool/security-headers-grader))
The final external check: does the site send modern security headers? WordPress doesn't include most of these by default, so the answer is usually "no". Adding them is a couple of `.htaccess` lines (Apache) or one nginx config block.
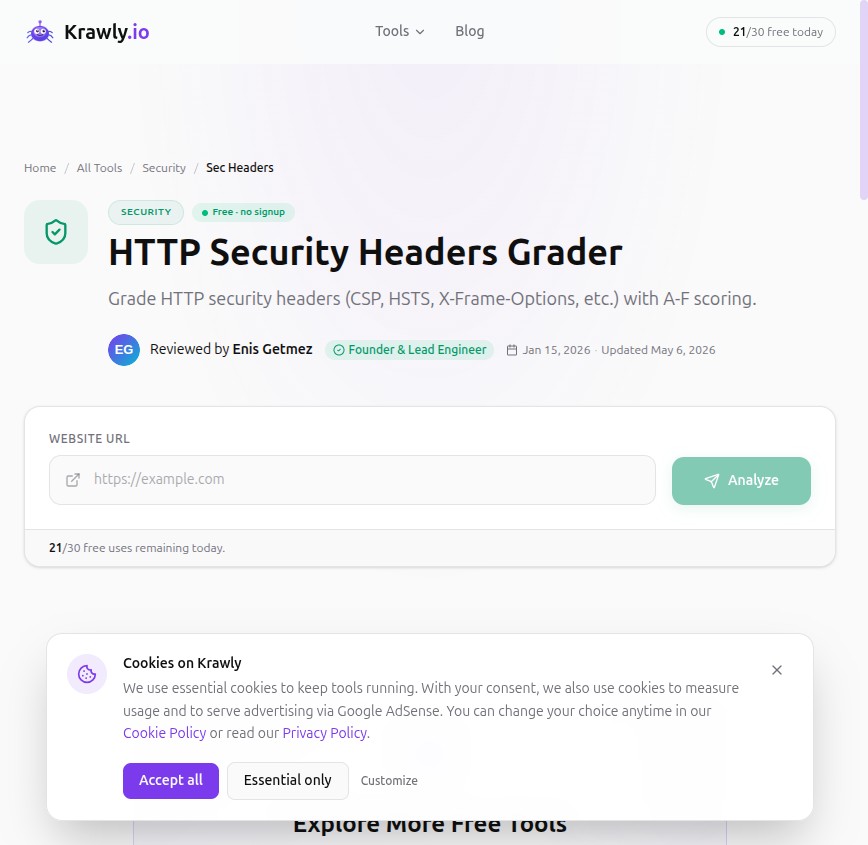
What I look for:
A grade of B or higher is achievable for any WordPress site with 15 minutes of `.htaccess` editing.
The 60-90 minute WordPress audit, summarized
For a typical small-business WordPress site:
1. Plugin inventory (5 min)
2. WordPress core + theme version check (2 min)
3. Meta + schema validation on homepage + top 3 traffic pages (15 min)
4. Page Speed analyzer + Lighthouse on homepage + 2 templates (15 min)
5. Broken link sweep on top 10 posts (20 min, mostly waiting)
6. Form spam + comment moderation check (5 min)
7. Heading-structure spot check on top 5 posts (10 min)
8. Security headers grade (5 min)
Total: 75-80 minutes. Report: 5-10 named issues with specific page URLs and specific fixes.
This is the kind of audit you can do for yourself once a quarter, or for a client as a $200-500 deliverable.
What this audit deliberately doesn't cover
External audits cannot see:
Those need admin access. If a client asks for "the full WordPress audit", schedule a follow-up with admin access for the internal audit too.
Methodology + corrections
This is a process I've refined over ~50 WordPress audits for clients between 2024 and 2026. The "8 tools" set is the minimum for an outside-in audit; some auditors use 12+. The tools I use are predominantly mine because they happen to be what's in front of me — substitute Wappalyzer for Plugin Detector, Lighthouse for Page Speed Analyzer, etc. if you prefer.
If you maintain a WordPress site and want me to (anonymously) include it in the next round of audit-pattern research, send the URL to info@krawly.io.